Cloud Network Firewall
In This Report
This is the first test of its kind in Cloud Network Firewall technology. The reports are provided in two ways: individual test reports for each vendor and a comparative report summarizing ratings and test results for all of the vendors in the test. While the overall Ratings are free to view, the individual test reports and the comparative report require a PAID Membership registration.
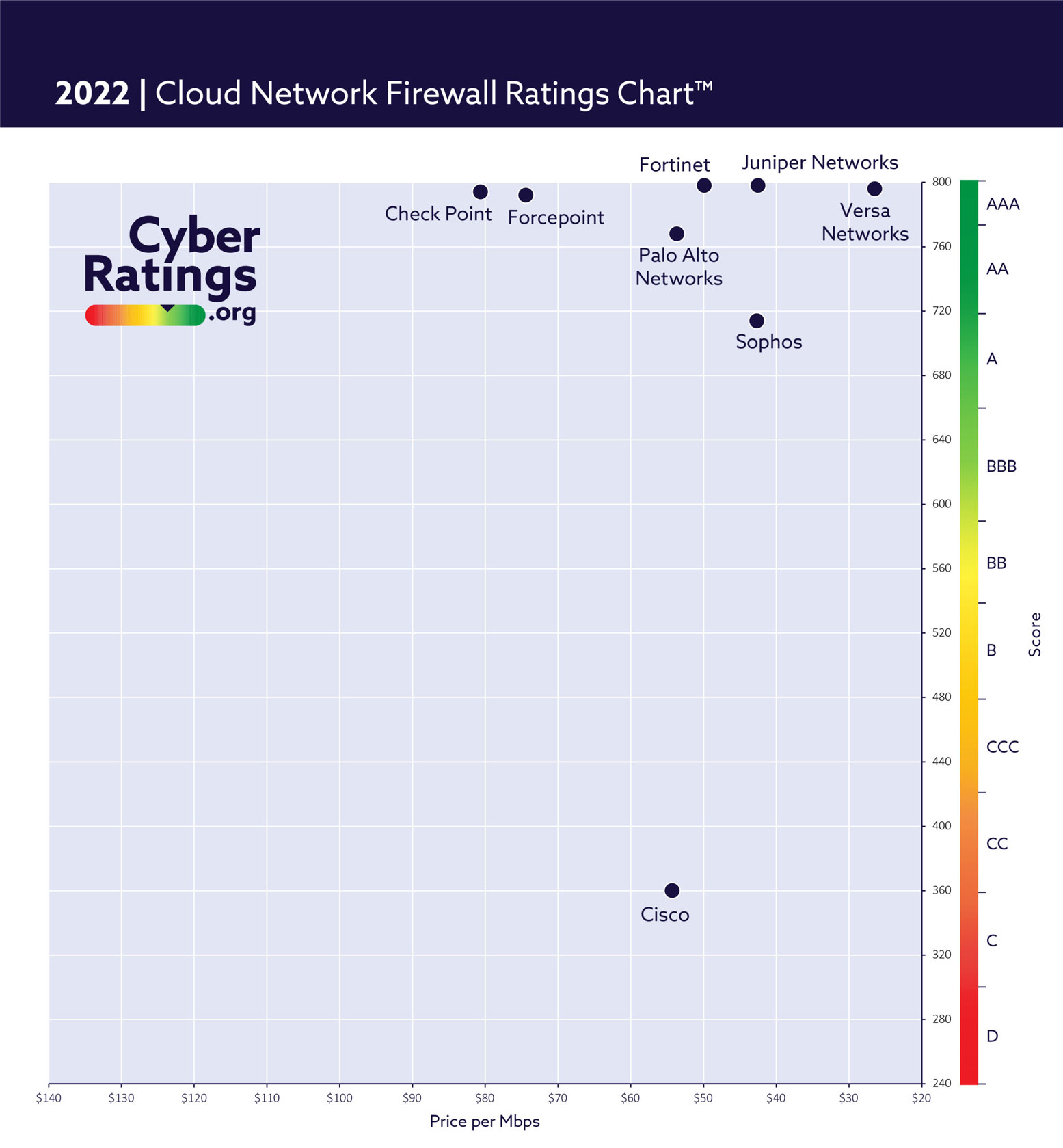
CyberRatings.org tested Management and Reporting Capabilities, Routing and Policy Enforcement, SSL/TLS Functionality, Threat Prevention and Performance.
Technology Overview
While the firewall market is one of the largest and most mature security technology segments, cloud network firewalls are relatively new. Firewalls have undergone several stages of development, from early packet filtering and circuit relay firewalls to application layer (proxy-based) and dynamic packet filtering firewalls. This is a new technology, deployed within a cloud service that by definition is constantly changing, protecting resources that are also deployed within that same cloud service.
We would like to issue a special thank you to Keysight for providing their CyPerf and Breaking Point tools for us to test Cloud Network Firewall.
We would also like to thank TeraPackets for providing us with their Threat Replayer tool.